THANK YOU FOR SUBSCRIBING
Get past These Five Cloud Security Myths and Lift Your Organization's Game
Cloud-Based solutions are providing enhanced security for all employees, security for applications, data and systems, and reduced complexity.
By
Apac CIOOutlook | Thursday, January 01, 1970
Stay ahead of the industry with exclusive feature stories on the top companies, expert insights and the latest news delivered straight to your inbox. Subscribe today.
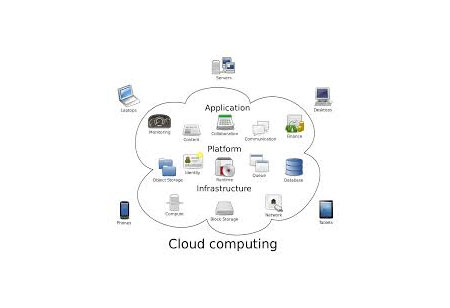
User privacy and data security are two major concerns of any IT infrastructure. Enterprises are adopting cloud-based security for greater flexibility and reduced complexity but there certain misconceptions that exist. There is reluctance amid many organizations to embrace cloud computing system but fear that these systems would be incapable of handling major security issues.
Cloud-Based solutions are providing enhanced security for all employees, security for applications, data and systems, and reduced complexity. Below are the five most common myths regarding the cloud-based security infrastructure.
1. Security certifications are only essential for cloud compliance department
Cloud-based security providers must have the necessary certifications, which should be checked by an organization before signing a contract. The security personnel of the organization must go through the agreement as a part of the initial vendor selection process.
2. Cloud provider data centers are always secure
It’s not apparent that the infrastructure provided by the cloud service is always reliable. Therefore, data center security managers must implement controls for data security which includes encryption, data loss prevention, and tokenization. The certification process from a third-party auditor can also ensure that requirements are met.
Check out: Top Cloud Security Companies
3. More data centers, better performance, and resiliency
The number of data centers has no to negligible impact on the performance of the cloud service provider; it’s a pure myth. Many big brands are having fewer data centers globally and are performing well whereas there are other organizations which are hundred in numbers but still cannot compete with the former.
4. Security of cloud service doesn’t impact cybersecurity insurance
Many organizations are investing in cyber protection. An organization will likely pay a lower cyber insurance premium if their respective cloud providers show certifications that demonstrate that the sensitive data is adequately secured.
5. External forces solely drive compliance
Even though a company has opted for a cloud security provider, the IT department is still responsible for shielding the organizational assets and also ensures compliance. Therefore, businesses must invest their time and resources that are needed to get compliance policies right and safeguard the information.





