THANK YOU FOR SUBSCRIBING
Protecting Data in the Cloud
The increasing adoption of cloud technology has given rise to a plethora of security concerns.
By
Apac CIOOutlook | Thursday, January 01, 1970
Stay ahead of the industry with exclusive feature stories on the top companies, expert insights and the latest news delivered straight to your inbox. Subscribe today.
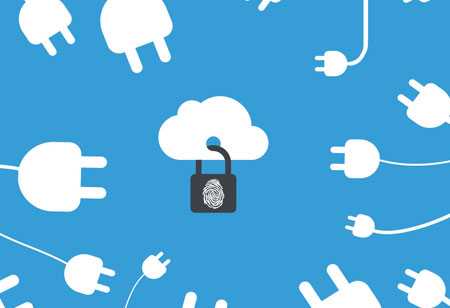
The increasing adoption of cloud technology has given rise to a plethora of security concerns. As several organizations store critical business information on the cloud, protecting that information from theft and data leakage becomes imperative. To protect the data from a security breach, most often than not data stored in the cloud is encrypted and would need an encryption key to unlock and access the information.
But who owns the key? The data can be stored either by the service provider or by individual users. Mostly, the cloud service provider has the key, allowing their systems to access and process user data. These services also access the key when a user logs in with a password, unlocking the data so the person can use it.
To maximize cloud storage security, most of the organizations are encrypting the data using their own encryption software before uploading it to the cloud. Subsequently, they upload the encoded file to the cloud. In order to get access to the file again, they will log in to the service, download it and decrypt it themselves. Another way to protect data against cybersecurity breach is to use authenticated encryption. This approach stores encrypted file, coupled with additional metadata that allows a user to detect whether the file has been modified since it was created.
Therefore, for those professionals who do not want to program their own tools, they have two choices: Identify authentic cloud storage service and download software that is open-source and has been well tested by independent security researchers. Or enterprises can leverage trusted open-source encryption software to encrypt their data before uploading it to the cloud; these are available for all operating systems and are generally free or very low-cost.
Check out: Top Cloud Solution Companies